flash
RAM
ROM
NVRAM
cisco certification 200-125 ccna exam preparation with practice questions and Answers
Which OSI layer manages data segments?
application layer
presentation layer
session layer
transport layer
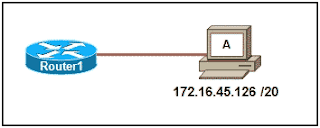
Refer to the exhibit. Which option correctly identifies the network address, range of host addresses, and the broadcast address for the network that contains host A?
Refer to the exhibit. Which option correctly identifies the network address, range of host addresses, and the broadcast address for the network that contains host A?
What is described by the network access layer of the TCP/IP model?
rules for packet acknowledgment, error recovery, and sequencing
rules for the handoff from the internet layer to the network access protocols
rules for how source and destination hosts exchange data between programs
rules for determining which processes can be used to route messages through an internetwork
rules for the handoff from the internet layer to the network access protocols
rules for how source and destination hosts exchange data between programs
rules for determining which processes can be used to route messages through an internetwork
Refer to the exhibit. A network technician wants to connect host A to the console of a Cisco switch to initialize the configuration. What type of cable is required for this connection?
straight-through cable
crossover cable
rollover cable
crossover cable
rollover cable
What can the user do from the command prompt, Router(config-line)# ?
Configure one of the network interfaces.
Configure one of the physical or virtual lines.
Verify the running configuration on the device.
Configure one of the physical or virtual lines.
Verify the running configuration on the device.
Which physical component is used to access and perform the initial configuration on a new unconfigured router?
Which physical component is used to access and perform the initial configuration on a new unconfigured router?
The tracert 10.1.3.2 command was issued on computer A. Computer A can ping other addresses on the local subnet. Computer A sent the first ICMP packet toward computer B with a TTL value of 1. A protocol analyzer that was running on computer B showed that the packet never reached its destination. Why did the packet not reach the destination?
The tracert 10.1.3.2 command was issued on computer A. Computer A can ping other addresses on the local subnet. Computer A sent the first ICMP packet toward computer B with a TTL value of 1. A protocol analyzer that was running on computer B showed that the packet never reached its destination. Why did the packet not reach the destination?
A user enters http://www.cisco.com/web1.htm in the address line of a browser. Which statement is true about this transaction?
The "http" portion indicates the protocol that is being used.
The "web1.htm" portion is the specific service name.
The retrieved web page will be displayed in URL code.
The "www.cisco.com" is the name of the web page file that is called
The "web1.htm" portion is the specific service name.
The retrieved web page will be displayed in URL code.
The "www.cisco.com" is the name of the web page file that is called
Refer to the exhibit. Communication for hosts X and Y is restricted to the local network. What is the reason for this?
Refer to the exhibit. Communication for hosts X and Y is restricted to the local network. What is the reason for this?
Refer to the exhibit. When host A sends a frame addressed for host D, which hosts will receive the frame?
Refer to the exhibit. When host A sends a frame addressed for host D, which hosts will receive the frame?
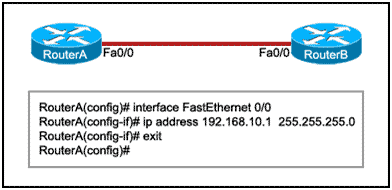
Refer to the exhibit. RouterB is configured properly. The Ethernet interface Fa0/0 of RouterA is configured with the use of the commands that are shown. However, a ping from the Fa0/0 interface of RouterA to the Fa0/0 interface of RouterB is unsuccessful. What action should be taken on RouterA to solve this problem?
Refer to the exhibit. RouterB is configured properly. The Ethernet interface Fa0/0 of RouterA is configured with the use of the commands that are shown. However, a ping from the Fa0/0 interface of RouterA to the Fa0/0 interface of RouterB is unsuccessful. What action should be taken on RouterA to solve this problem?
What two conclusions are evident from these commands? (Choose two.)
Users who attempt to connect to the console port of the router must enter a password.
The entries permit access through the console by the use of j1mdi2 as the password.
The entries eliminate the need for authentication.
Access through the console will be denied because the console configuration is incomplete.
The entries prevent passwords from being displayed as plain text.
The entries permit access through the console by the use of j1mdi2 as the password.
The entries eliminate the need for authentication.
Access through the console will be denied because the console configuration is incomplete.
The entries prevent passwords from being displayed as plain text.
Which two types of media can provide bandwidth up to 1 Gb/s? (Choose two.)
10 BASE-T
100 BASE-T
100 BASE-FX
1000 BASE-TX
1000 BASE-SX
100 BASE-T
100 BASE-FX
1000 BASE-TX
1000 BASE-SX
Refer to the exhibit. An employee wants to access the organization intranet from home. Which intermediary device should be used to connect the organization intranet to the Internet to enable this access?
Refer to the exhibit. An employee wants to access the organization intranet from home. Which intermediary device should be used to connect the organization intranet to the Internet to enable this access?
An organization has been assigned network ID 10.10.128.0 and subnet mask 255.255.224.0. Which IP address range can be used for this organization?
10.10.128.0 to 10.10.160.255
10.10.128.0 to 10.10.159.255
10.10.128.0 to 10.10.192.255
10.10.128.0 to 10.10.0.159
10.10.128.0 to 10.10.159.0
10.10.128.0 to 10.10.159.255
10.10.128.0 to 10.10.192.255
10.10.128.0 to 10.10.0.159
10.10.128.0 to 10.10.159.0
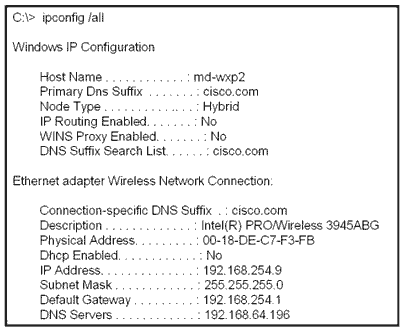
Refer to the exhibit. A technician is working on a network problem that requires verification of the router LAN interface. What address should be pinged from this host to confirm that the router interface is operational?
Refer to the exhibit. A technician is working on a network problem that requires verification of the router LAN interface. What address should be pinged from this host to confirm that the router interface is operational?
Which prompt represents the appropriate mode used for the copy running-config startup-config command ?
Switch-6J>
Switch-6J#
Switch-6J(config)#
Switch-6J(config-if)#
Switch-6J(config-line)#
Switch-6J#
Switch-6J(config)#
Switch-6J(config-if)#
Switch-6J(config-line)#
Refer to the exhibit. Host A attempts to establish a TCP/IP session with host C. During this attempt, a frame was captured with the source MAC address 0050.7320.D632 and the destination MAC address 0030.8517.44C4. The packet inside the captured frame has an IP source address 192.168.7.5, and the destination IP address is 192.168.219.24. At which point in the network was this packet captured?
Refer to the exhibit. Host A attempts to establish a TCP/IP session with host C. During this attempt, a frame was captured with the source MAC address 0050.7320.D632 and the destination MAC address 0030.8517.44C4. The packet inside the captured frame has an IP source address 192.168.7.5, and the destination IP address is 192.168.219.24. At which point in the network was this packet captured?
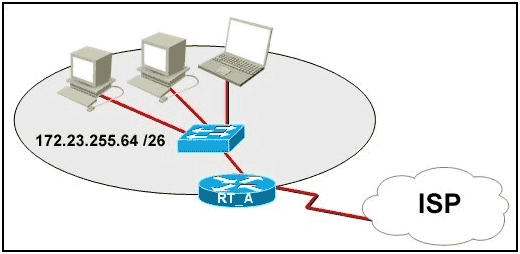
Refer to the exhibit. What function does router RT_A need to provide to allow Internet access for hosts in this network?
Refer to the exhibit. What function does router RT_A need to provide to allow Internet access for hosts in this network?
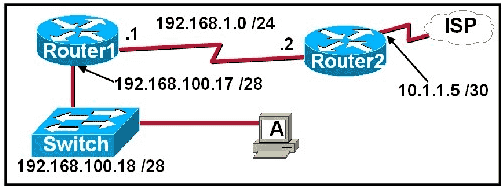
Refer to the exhibit. A network technician is trying to determine the correct IP address configuration for Host A. What is a valid configuration for Host A?
Refer to the exhibit. A network technician is trying to determine the correct IP address configuration for Host A. What is a valid configuration for Host A?
IP address: 192.168.100.19; Subnet Mask: 255.255.255.248; Default Gateway: 192.16.1.2IP address: 192.168.100.20; Subnet Mask: 255.255.255.240; Default Gateway: 192.168.100.17
IP address: 192.168.100.21; Subnet Mask: 255.255.255.248; Default Gateway: 192.168.100.18
IP address: 192.168.100.22; Subnet Mask: 255.255.255.240; Default Gateway: 10.1.1.5
IP address: 192.168.100.30; Subnet Mask: 255.255.255.240; Default Gateway: 192.168.1.1
IP address: 192.168.100.31; Subnet Mask: 255.255.255.240; Default Gateway: 192.168.100.1
When must a router serial interface be configured with the clock rate command?
when the interface is functioning as a DTE device
when the interface timers have been cleared
when the connected DTE device is shut down
when the interface is functioning as a DCE device
when the interface timers have been cleared
when the connected DTE device is shut down
when the interface is functioning as a DCE device
Which subnet mask would be assigned to the network address of 192.168.32.0 to provide 254 useable host addresses per subnetwork?
255.255.0.0
255.255.255.0
255.255.254.0
255.255.248.0
Refer to the exhibit. Assume that all devices are using default settings. How many subnets are required to address the topology that is shown?
Refer to the exhibit. Assume that all devices are using default settings. How many subnets are required to address the topology that is shown?
Which option identifies the primary interface which would be used for initial configuration of a Cisco router?
AUX interface
Ethernet interface
serial interface
console interface
What are three common methods for setting a UTP Ethernet port to MDI or MDIX operation? (Choose three.)
direct configuration of the device
cable color code association
cable selection and configuration
use of cable testers to determine pinouts
the enabling of the mechanism to electrically swap the transmit and receive pairs
the automatic detection and negotiating of MDI/MDIX operation of the port
What type of network cable is used between a terminal and a console port?
cross-over
straight-through
rollover
patch cable
Refer to the exhibit. A network technician has been allocated the 192.168.1.0/24 private IP address range for use in the network that shown in the exhibit. Which subnet mask would be used to meet the host requirements for segment A of this internetwork?
Refer to the exhibit. A network technician has been allocated the 192.168.1.0/24 private IP address range for use in the network that shown in the exhibit. Which subnet mask would be used to meet the host requirements for segment A of this internetwork?
255.255.255.128255.255.255.192
255.255.255.224
255.255.255.240
255.255.255.248
To establish a console connection from a computer to a Cisco router, which cable wiring option would be used?
crossover cable
straight through cable
rollover cable
V.35 cable
Refer to the exhibit. A student is setting up a home network primarily used for extensive file transfers, streaming video, and gaming. Which network device is best suited to these types of activities in the topology shown?
Refer to the exhibit. A student is setting up a home network primarily used for extensive file transfers, streaming video, and gaming. Which network device is best suited to these types of activities in the topology shown?
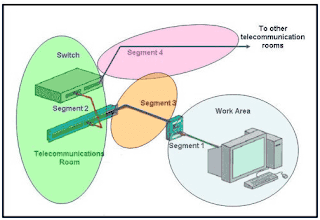
Refer to the exhibit. Which three statements identify the type of cabling that would be used in the segments that are shown? (Choose three.)
Refer to the exhibit. Which three statements identify the type of cabling that would be used in the segments that are shown? (Choose three.)
What does the term “attenuation” mean in data communication?
loss of signal strength as distance increases
time for a signal to reach its destination
leakage of signals from one cable pair to another
strengthening of a signal by a networking device
Refer to the exhibit. What destination IP address will PC1 place in the header for a packet destined for PC2?
Refer to the exhibit. What destination IP address will PC1 place in the header for a packet destined for PC2?
Refer to the exhibit. Based on the IP configuration shown, what would be the result of Host A and Host B attempting to communicate outside the network segment?
Refer to the exhibit. Based on the IP configuration shown, what would be the result of Host A and Host B attempting to communicate outside the network segment?
both host A and B would be successful
host A would be successful, host B would fail
host B would be successful, host A would fail
both Host A and B would fail
Which three types of connectors are commonly associated with Cisco’s V.35 serial cables? (Choose three.)
RJ 11
DB 60
Winchester 15 pin
DB 9
smart serial
RJ 45
Refer to the exhibit. Which three statements are true about the exhibited topology? (Choose three.)
Hosts B and C are in the same subnet.
Five broadcast domains are present.
Host B is using a crossover cable to connect to the router.
Four broadcast domains are present.
Five networks are shown.
Host B is using a rollover cable to connect to the router.
Refer to the exhibit. A student working in the lab selects a cable that is wired as shown. Which connection types can successfully be made with this cable? (Choose two.)
connecting a PC to a router’s console port
connecting two routers together via their fast ethernet ports
connecting two switches together at gigabit speeds
connecting a PC to a switch at Gigabit Ethernet speeds
connecting two devices with the same interface type at Fast Ethernet speeds
A company is planning to subnet its network for a maximum of 27 hosts. Which subnet mask would provide the needed hosts and leave the fewest unused addresses in each subnet?
255.255.255.0
255.255.255.192
255.255.255.224
255.255.255.240
255.255.255.248
What are two common methods for setting a UTP Ethernet port to MDI or MDIX operation? (Choose two.)
cable color code association
cable selection and configuration
use of cable testers to determine pinouts
the automatic detection and negotiating of MDI/MDIX operation of the port
the enabling of the mechanism to electrically swap the transmit and receive pairs
cable selection and configuration
use of cable testers to determine pinouts
the automatic detection and negotiating of MDI/MDIX operation of the port
the enabling of the mechanism to electrically swap the transmit and receive pairs
Refer to the exhibit. A network administrator has decided to use packet capture software to evaluate all traffic from the student subnet on the way to the Internet. To ensure that all packets are captured, what network device should be used to connect the monitoring station to the network between R1 and R2?
Which three statements are true about the role of routers in the network? (Choose three.)
They propagate broadcasts.
They enlarge collision domains.
They segment broadcast domains.
They interconnect different network technologies.
Each router interface requires a separate network or subnet.
They maintain a common frame format between LAN and WAN interfaces.
A network administrator is required to use media in the network that can run up to 100 meters in cable length without using repeaters. The chosen media must be inexpensive and easily installed. The installation will be in a pre-existing building with limited cabling space. Which type of media would best meet these requirements?
STP
UTP
coaxial
single-mode fiber
multimode fiber
UTP
coaxial
single-mode fiber
multimode fiber
What makes fiber preferable to copper cabling for interconnecting buildings? (Choose three.)
greater distances per cable run
lower installation cost
limited susceptibility to EMI/RFI
durable connections
greater bandwidth potential
easily terminated
lower installation cost
limited susceptibility to EMI/RFI
durable connections
greater bandwidth potential
easily terminated
What does the IEEE 802.2 standard represent in Ethernet technologies?
MAC sublayer
Physical layer
Logical Link
Control sublayer
Network layer
Physical layer
Logical Link
Control sublayer
Network layer
Ethernet operates at which layer of the TCP/IP network model?
application
physical
transport
internet
data link
network access
physical
transport
internet
data link
network access
Refer to the exhibit. What command was executed on a host computer to produce the results shown?
route PRINT
arp –a
arp –d
netstat
telnet
arp –a
arp –d
netstat
telnet
Ethernet operates at which layers of the OSI model? (Choose two.)
Network layer
Transport layer
Physical layer
Application layer
Session layer
Data-link layer
Refer to the exhibit. Host_A is attempting to contact Server_B. Which statements correctly describe the addressing Host_A will generate in the process? (Choose two.)
Refer to the exhibit. Host_A is attempting to contact Server_B. Which statements correctly describe the addressing Host_A will generate in the process? (Choose two.)
A packet with the destination IP of Router_B.
A frame with the destination MAC address of Switch_A.
A packet with the destination IP of Router_A.
A frame with the destination MAC address of Router_A.
A packet with the destination IP of Server_B.
A frame with the destination MAC address of Server_B.
Refer to the exhibit. The switch and workstation are administratively configured for full-duplex operation. Which statement accurately reflects the operation of this link?
Refer to the exhibit. The switch and workstation are administratively configured for full-duplex operation. Which statement accurately reflects the operation of this link?
Which two features make switches preferable to hubs in Ethernet-based networks? (Choose two.)
reduction in cross-talk
minimizing of collisions
support for UTP cabling
division into broadcast domains
increase in the throughput of communications
After an Ethernet collision, when the backoff algorithm is invoked, which device has priority to transmit data?
the device involved in the collision with the lowest MAC address
the device involved in the collision with the lowest IP address
any device in the collision domain whose backoff timer expires first
those that began transmitting at the same time
Which of the following is a drawback of the CSMA/CD access method?
Collisions can decrease network performance.
It is more complex than non-deterministic protocols.
Deterministic media access protocols slow network performance.
CSMA/CD LAN technologies are only available at slower speeds than other LAN technologies.
It is more complex than non-deterministic protocols.
Deterministic media access protocols slow network performance.
CSMA/CD LAN technologies are only available at slower speeds than other LAN technologies.
Which of the following describe interframe spacing? (Choose two.)
the minimum interval, measured in bit-times, that any station must wait before sending another frame
the maximum interval, measured in bit-times, that any station must wait before sending another frame
the 96-bit payload padding inserted into a frame to achieve a legal frame size
the 96-bit frame padding transmitted between frames to achieve proper synchronization
the time allowed for slow stations to process a frame and prepare for the next frame
the maximum interval within which a station must send another frame to avoid being considered unreachable
the maximum interval, measured in bit-times, that any station must wait before sending another frame
the 96-bit payload padding inserted into a frame to achieve a legal frame size
the 96-bit frame padding transmitted between frames to achieve proper synchronization
the time allowed for slow stations to process a frame and prepare for the next frame
the maximum interval within which a station must send another frame to avoid being considered unreachable
Refer to the exhibit. Which option correctly identifies content that the frame data field may contain?
Refer to the exhibit. Which option correctly identifies content that the frame data field may contain?
preamble and stop frame
network layer packet
physical addressing
FCS and SoF
What is the primary purpose of ARP?
translate URLs to IP addresses
resolve IPv4 addresses to MAC addresses
provide dynamic IP configuration to network devices
convert internal private addresses to external public addresses
resolve IPv4 addresses to MAC addresses
provide dynamic IP configuration to network devices
convert internal private addresses to external public addresses
What are three functions of the upper data link sublayer in the OSI model? (Choose three.)
recognizes streams of bits
identifies the network layer protocol
makes the connection with the upper layers
identifies the source and destination applications
insulates network layer protocols from changes in physical equipment
determines the source of a transmission when multiple devices are transmitting
identifies the network layer protocol
makes the connection with the upper layers
identifies the source and destination applications
insulates network layer protocols from changes in physical equipment
determines the source of a transmission when multiple devices are transmitting
In the graphic, Host A has reached 50% completion in sending a 1 KB Ethernet frame to Host D when Host B wishes to transmit its own frame to Host C. What must Host B do?
In the graphic, Host A has reached 50% completion in sending a 1 KB Ethernet frame to Host D when Host B wishes to transmit its own frame to Host C. What must Host B do?
Host B can transmit immediately since it is connected on its own cable segment.Host B must wait to receive a CSMA transmission from the hub, to signal its turn.
Host B must send a request signal to Host A by transmitting an interframe gap.
Host B must wait until it is certain that Host A has completed sending its frame.
What three primary functions does data link layer encapsulation provide? (Choose three.)
addressing
error detection
frame delimiting
port identification
path determination
IP address resolution
error detection
frame delimiting
port identification
path determination
IP address resolution
Host A has an IP address of 172.16.225.93 and a mask of 255.255.248.0. Host A needs to communicate with a new host whose IP is 172.16.231.78. Host A performs the ANDing operation on the destination address. What two things will occur? (Choose two.)
Host A will change the destination IP to the IP of the nearest router and forward the packet.
Host A will broadcast an ARP request for the MAC of its default gateway.
A result of 172.16.225.0 will be obtained.
Host A will broadcast an ARP request for the MAC of the destination host.
A result of 172.16.224.0 will be obtained.
A result of 172.16.225.255 will be obtained.
Host A will broadcast an ARP request for the MAC of its default gateway.
A result of 172.16.225.0 will be obtained.
Host A will broadcast an ARP request for the MAC of the destination host.
A result of 172.16.224.0 will be obtained.
A result of 172.16.225.255 will be obtained.
What are the two most commonly used media types in Ethernet networks today? (Choose two.)
coaxial thicknet
copper UTP
coaxial thinnet
optical fiber
shielded twisted pair
copper UTP
coaxial thinnet
optical fiber
shielded twisted pair
How to view linux command history | linux history command in terminal
How to view Linux Terminal History
Command : history
Using Linux history Command You Can View Linux Command History in Linux terminal.
 |
| Show Terminal Command History Using History Command in Linux |
View Current Logged in User in Linux | Linux whoami Command
View Linux Current User
Command : whoami
To View Current Logged in User in Linux you can use whoami command in terminal in you're Linux Computer.example whoami Command
In example above whoami command returns user as the Current Logged In User.
How To Check SELinux Status | SELinux Commands In Linux
How To Check SELinux Status In Linux
Command : sestatusUse sestatus Command to Check SELinux Status In You're CentOS Linux Machine.
How to Check Centos Version | Determine Centos Version
How to Get Centos Version
You Can Use cat /etc/centos-release Command.Also Using cat /etc/redhat-release and cat /etc/*release* Command You can find centos version of your Computer
Example
cat /etc/centos-release
Above example Shows current version of the Centos Machine as CentOS release 6.3 (Final)When a collision occurs in a network using CSMA/CD, how do hosts with data to transmit respond after the backoff period has expired?
The hosts return to a listen-before-transmit mode.
The hosts creating the collision have priority to send data.
The hosts creating the collision retransmit the last 16 frames.
The hosts extend their delay period to allow for rapid transmission
Which statements correctly describe MAC addresses? (Choose three.)
dynamically assigned
copied into RAM during system startup
layer 3 address
contains a 3 byte OUI
6 bytes long
32 bits long
copied into RAM during system startup
layer 3 address
contains a 3 byte OUI
6 bytes long
32 bits long
Why do hosts on an Ethernet segment that experience a collision use a random delay before attempting to transmit a frame?
A random delay is used to ensure a collision-free link.
A random delay value for each device is assigned by the manufacturer.
A standard delay value could not be agreed upon among networking device vendors.
A random delay helps prevent the stations from experiencing another collision during the transmission.
A random delay value for each device is assigned by the manufacturer.
A standard delay value could not be agreed upon among networking device vendors.
A random delay helps prevent the stations from experiencing another collision during the transmission.
Refer to the exhibit. Which type of Category 5 cable is used to make an Ethernet connection between Host A and Host B?
coax cable
rollover cable
crossover cable
straight-through cable
Which OSI layer is responsible for binary transmission, cable specification, and physical aspects of network communication?
Presentation
Transport
Data Link
Physical
Transport
Data Link
Physical
What is considered a benefit of wireless as a media choice?
more host mobility
lower security risks
reduced susceptibility to interference
less impact of the surroundings on the effective coverage area
lower security risks
reduced susceptibility to interference
less impact of the surroundings on the effective coverage area
With the use of unshielded twisted-pair copper wire in a network, what causes crosstalk within the cable pairs?
the magnetic field around the adjacent pairs of wire
the use of braided wire to shield the adjacent wire pairs
the reflection of the electrical wave back from the far end of the cable
the collision caused by two nodes trying to use the media simultaneously
the use of braided wire to shield the adjacent wire pairs
the reflection of the electrical wave back from the far end of the cable
the collision caused by two nodes trying to use the media simultaneously
What are three measures of data transfer? (Choose three.)
goodput
frequency
amplitude
throughput
crosstalk
bandwidth
frequency
amplitude
throughput
crosstalk
bandwidth
Which characteristics describe fiber optic cable? (Choose two.)
It is not affected by EMI or RFI.
Each pair of cables is wrapped in metallic foil.
It combines the technique of cancellation, shielding and twisting to protect data.
It has a maximum speed of 100 Mbps.
It is the most expensive type of LAN cabling.
Each pair of cables is wrapped in metallic foil.
It combines the technique of cancellation, shielding and twisting to protect data.
It has a maximum speed of 100 Mbps.
It is the most expensive type of LAN cabling.
What is a possible effect of improperly applying a connector to a network cable?
Data will be forwarded to the wrong node.
Data transmitted through that cable may experience signal loss.
An improper signaling method will be implemented for data transmitted on that cable.
The encoding method for data sent on that cable will change to compensate for the improper connection.
Data transmitted through that cable may experience signal loss.
An improper signaling method will be implemented for data transmitted on that cable.
The encoding method for data sent on that cable will change to compensate for the improper connection.
Which method of signal transmission uses radio waves to carry signals?
electrical
optical
wireless
acoustic
show interface status Cisco command reference basic Cisco configuration
Command :show interfaces status
Use In : Privileged EXEC Mode
Cisco IOS Command show interfaces status use in switches to view current status of switch ports use full command to switch port monitor.Should be used on privileged EXEC mode
It shows the port name port description, Witch Vlan switch ports belongs to (by default all switch ports belongs to Vlan1), type of port, speed of the ports, current status of the switch ports and the duplex mode (full duplex or half duplex)

What is a primary role of the Physical layer in transmitting data on the network?
create the signals that represent the bits in each frame on to the media
provide physical addressing to the devices
determine the path packets take through the network
control data access to the media
An installed fiber run can be checked for faults, integrity, and the performance of the media by using what device?
light injector
OTDR
TDR
multimeter
OTDR
TDR
multimeter
What characteristic of UTP cable helps reduce the effects of interference?
the metal braiding in the shielding
the reflective cladding around core
the twisting of the wires in the cable
the insulating material in the outer jacket
Which of the following is a characteristic of single-mode fiber-optic cable?
generally uses LEDs as the light source
relatively larger core with multiple light paths
less expensive than multimode
generally uses lasers as the light source
When is a straight-through cable used in a network?
when connecting a router through the console port
when connecting one switch to another switch
when connecting a host to a switch
when connecting a router to another router
In most business LANs, which connector is used with twisted-pair networking cable?
BNC
RJ-11
RJ-45
Type F
Which type of cable run is most often associated with fiber-optic cable?
backbone cable
horizontal cable
patch cable
work area cable
horizontal cable
patch cable
work area cable
What statements are true regarding addresses found at each layer of the OSI model? (Choose two.)
Layer 2 may identify devices by a physical address burned into the network card
Layer 2 identifies the applications that are communicating
Layer 3 represents a hierarchical addressing scheme
Layer 4 directs communication to the proper destination network
Layer 4 addresses are used by intermediary devices to forward data
Layer 2 identifies the applications that are communicating
Layer 3 represents a hierarchical addressing scheme
Layer 4 directs communication to the proper destination network
Layer 4 addresses are used by intermediary devices to forward data
Which three factors should be considered when implementing a Layer 2 protocol in a network? (Choose three.)
the Layer 3 protocol selected
the geographic scope of the network
the PDU defined by the transport layer
the physical layer implementation
the number of hosts to be interconnected
What determines the method of media access control? (Choose two.)
network layer addressing
media sharing
application processes
logical topology
intermediary device function
What is a function of the data link layer?
provides the formatting of data
provides end-to-end delivery of data between hosts
provides delivery of data between two applications
provides for the exchange data over a common local media
What is a characteristic of a logical point-to-point topology?
The nodes are physically connected.
The physical arrangement of the nodes is restricted.
The media access control protocol can be very simple.
The data link layer protocol used over the link requires a large frame header.
The physical arrangement of the nodes is restricted.
The media access control protocol can be very simple.
The data link layer protocol used over the link requires a large frame header.
A network administrator has been asked to provide a graphic representation of exactly where the company network wiring and equipment are located in the building. What is this type of drawing?
logical topology
physical topology
cable path
wiring grid
access topology
What are three characteristics of valid Ethernet Layer 2 addresses? (Choose three.)
They are 48 binary bits in length.
They are considered physical addresses.
They are generally represented in hexadecimal format.
They consist of four eight-bit octets of binary numbers.
They are used to determine the data path through the network.
They must be changed when an Ethernet device is added or moved within the network.
They are considered physical addresses.
They are generally represented in hexadecimal format.
They consist of four eight-bit octets of binary numbers.
They are used to determine the data path through the network.
They must be changed when an Ethernet device is added or moved within the network.
What two facts are true when a device is moved from one network or subnet to another? (Choose two.)
The Layer 2 address must be reassigned.
The default gateway address should not be changed.
The device will still operate at the same Layer 2 address.
Applications and services will need additional port numbers assigned.
The Layer 3 address must be reassigned to allow communications to the new network.
The default gateway address should not be changed.
The device will still operate at the same Layer 2 address.
Applications and services will need additional port numbers assigned.
The Layer 3 address must be reassigned to allow communications to the new network.
Which statements describe the logical token-passing topology? (Choose two.)
Network usage is on a first come, first serve basis.
Computers are allowed to transmit data only when they possess a token.
Data from a host is received by all other hosts.
Electronic tokens are passed sequentially to each other.
Token passing networks have problems with high collision rates.
Computers are allowed to transmit data only when they possess a token.
Data from a host is received by all other hosts.
Electronic tokens are passed sequentially to each other.
Token passing networks have problems with high collision rates.
What is the purpose of the preamble in an Ethernet frame?
is used as a pad for data
identifies the source address
identifies the destination address
marks the end of timing information
is used for timing synchronization with alternating patterns of ones and zeros
identifies the source address
identifies the destination address
marks the end of timing information
is used for timing synchronization with alternating patterns of ones and zeros
Refer to the exhibit. A frame is being sent from the PC to the laptop. Which source MAC and IP addresses will be included in the frame as it leaves RouterB? (Choose two.)
Refer to the exhibit. A frame is being sent from the PC to the laptop. Which source MAC and IP addresses will be included in the frame as it leaves RouterB? (Choose two.)
source MAC – PC
source MAC – S0/0 on RouterA
source MAC – Fa0/1 on RouterB
source IP – PC
source IP – S0/0 on RouterA
source IP – Fa0/1 of RouterB
Refer to the exhibit. How many unique CRC calculations will take place as traffic routes from the PC to the laptop?
Refer to the exhibit. How many unique CRC calculations will take place as traffic routes from the PC to the laptop?
What is the primary purpose of the trailer in a data link layer frame?
define the logical topology
provide media access control
support frame error detection
carry routing information for the frame
provide media access control
support frame error detection
carry routing information for the frame
What is true regarding media access control? (Choose three.)
Ethernet utilizes CSMA/CD
defined as placement of data frames on the media
contention-based access is also known as deterministic
802.11 utilizes CSMA/CD
Data Link layer protocols define the rules for access to different media
controlled access contains data collisions
defined as placement of data frames on the media
contention-based access is also known as deterministic
802.11 utilizes CSMA/CD
Data Link layer protocols define the rules for access to different media
controlled access contains data collisions
What is true concerning physical and logical topologies?
The logical topology is always the same as the physical topology.
Physical topologies are concerned with how a network transfers frames.
Physical signal paths are defined by Data Link layer protocols.
Logical topologies consist of virtual connections between nodes.
Physical topologies are concerned with how a network transfers frames.
Physical signal paths are defined by Data Link layer protocols.
Logical topologies consist of virtual connections between nodes.
What is a primary purpose of encapsulating packets into frames?
provide routes across the internetwork
format the data for presentation to the user
facilitate the entry and exit of data on media
identify the services to which transported data is associated
Which options are properties of contention-based media access for a shared media? (Choose three.)
non-deterministic
less overhead
one station transmits at a time
collisions exist
devices must wait their turn
token passing
less overhead
one station transmits at a time
collisions exist
devices must wait their turn
token passing
Which IPv4 subnetted addresses represent valid host addresses? (Choose three.)
172.16.4.127 /26
172.16.4.155 /26
172.16.4.193 /26
172.16.4.95 /27
172.16.4.159 /27
172.16.4.207 /27
172.16.4.155 /26
172.16.4.193 /26
172.16.4.95 /27
172.16.4.159 /27
172.16.4.207 /27
What is the primary reason for development of IPv6?
security
header format simplification
expanded addressing capabilities
addressing simplification
header format simplification
expanded addressing capabilities
addressing simplification
Refer to the exhibit. Host A is connected to the LAN, but it cannot get access to any resources on the Internet. The configuration of the host is shown in the exhibit. What could be the cause of the problem?
The host subnet mask is incorrect.
The default gateway is a network address.
The default gateway is a broadcast address.
The default gateway is on a different subnet from the host.
Which statements are true regarding IP addressing? (Choose two.) NAT translates public addresses to private addresses destined for the Internet.
Only one company is allowed to use a specific private network address space.
Private addresses are blocked from public Internet by router.
Network 172.32.0.0 is part of the private address space.
IP address 127.0.0.1 can be used for a host to direct traffic to itself.
Private addresses are blocked from public Internet by router.
Network 172.32.0.0 is part of the private address space.
IP address 127.0.0.1 can be used for a host to direct traffic to itself.
What is a group of hosts called that have identical bit patterns in the high order bits of their addresses?
an internet
a network
an octet
a radi
a network
an octet
a radi
Subscribe to:
Comments (Atom)
Popular Posts
-
VTY interface console interface Ethernet interface secret EXEC mode privileged EXEC mode router configuration mode
-
Refer to the exhibit. Host_A is attempting to contact Server_B. Which statements correctly describe the addressing Host_A will generate ...
-
Refer to the exhibit. What two commands will change the next-hop address for the 10.0.0.0/8 network from 172.16.40.2 to 192.168.1.2? (C...
-
forwarding rate traffic flow analysis expected future growth number of required core connections number of hubs that are needed in the acces...
-
An additional subnet is required for a new Ethernet link between Router1 and Router2 as shown in the diagram. Which of the following su...
-
32-bit address next hop router interface subnet mask unicast host address Layer 2 address
-
Transport Data Link Session Network Physical
-
WinterPark(config)# ip route 0.0.0.0 0.0.0.0 192.168.146.1 Altamonte(config)# ip route 10.0.234.0 255.255.255.0 192.168.146.2 Altamonte(c...
-
Refer to the exhibit. Routers R1 and R2 are directly connected via their serial interfaces and are both running the EIGRP routing protocol...
-
Cisco CCNA Routing and Switching 200-120 Official Cert Guide Library By Wendell Odom Pages: 1600 Publisher Cisco Press Cisco CCNA R...

















.jpg)



















